Member-only story
Exploring AWS Shield: Defending Against Network Volumetric, Protocol, and Application Layer Attacks
AWS Shield Standard and AWS Shield Advanced are security services offered by Amazon Web Services (AWS) to safeguard AWS resources from Distributed Denial of Service (DDoS) attacks. These attacks occur when multiple compromised systems attempt to inundate a target with excessive traffic, disrupting its normal functioning. DDoS attacks can impede legitimate users from accessing services and potentially cause the target to crash due to an overwhelming volume of traffic.
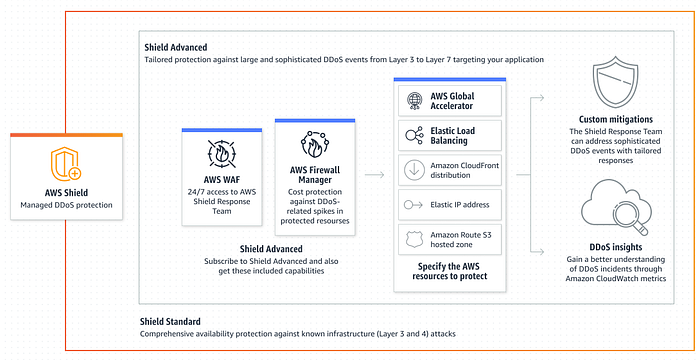
Protection is offered at different layers of the network stack, specifically at the network and transport layers (layer 3 and 4), as well as at the application layer (layer 7). The network and transport layer protection addresses attacks that exploit vulnerabilities in the lower levels of the network stack, while the application layer protection focuses on safeguarding against more sophisticated attacks that target the specific applications running on the server.
AWS Shield is equipped to defend against a broad spectrum of both known and unknown DDoS attack vectors. Known vectors are those that are recognized and documented, while zero-day attack vectors are newly discovered threats that may not have been identified by security services at the time of detection. The detection and mitigation mechanisms of AWS Shield are designed to provide comprehensive coverage, offering protection even against threats that are not explicitly known to the service when detected.
Notably, AWS Shield Standard is automatically included at no additional cost when utilizing AWS services, ensuring that users benefit from baseline protection against DDoS attacks as part of their AWS subscription. This ensures that AWS customers have a foundational level of security to mitigate the impact of potential DDoS threats on their resources.
Network volumetric attacks (layer 3)
Network volumetric attacks, falling under the umbrella of infrastructure layer attack vectors, constitute a specific type of threat at the layer 3 level. These attack vectors aim to overwhelm the targeted network or resource by flooding it with an excessive volume of traffic. The primary objective is to exhaust the available…
